How Secure Are Your Process Safety Systems?
Cybersecurity is playing an increasingly important role in process safety systems. This became quite apparent with the cyber-attack on a safety system late in 2017 that ultimately ended in the safe shutdown of a Middle Eastern petrochemical facility. Process safety systems provide the last line of defense to shut down a plant safely in the event of an abnormal situation. Attacks on safety systems have the potential to cause real harm in the physical world, so it’s important that ICS/SCADA cybersecurity policy include rational approaches to process safety systems.
However, the scope of safety and cybersecurity goes well beyond process safety systems alone. Across the industrial and infrastructure worlds, an increasing number of end users are adopting more sophisticated strategies for risk management. This drives closer cooperation and convergence between the safety and cybersecurity disciplines.
This convergence manifests itself in several ways. An increased focus on risk management helps end users justify increased spending on cybersecurity. Many end users are adopting the concepts of process hazard analysis (PHA) and hazard operability analysis (HAZOP). Suppliers are obliging with cyber-focused services that incorporate key concepts from PHA and HAZOP. These include layers of protection analysis (LOPA) and risk matrices that analyze the consequence and severity of actions in operating environments.
Cost and Impact of Cyber Incidents vs. Safety Incidents
At the operational technology (OT) level, both cybersecurity- and safety-related projects can be challenging to cost justify and thus gain approval. Both domains protect against what could happen to help avoid a cyber-attack or plant incident. The financial impact of either could be massive.
The BP Deepwater Horizon oil spill, for example, is estimated to have cost the company $65 billion in cleanup costs, legal fees and fines.
The cost of cyber incidents can be just as damaging, with a simple ransomware attack costing an average of $5 million for companies across the board. The impact on industrial plants and facilities, however, is much greater. In 2017, a Tokyo-area Honda plant was forced to shut down because of WannaCry ransomware. In this case, the plant controls were not compromised, but the ransomware attack was virulent enough to shut down operations in a plant that produces around 1,000 vehicles a day.
Even if a refinery or chemical plant is able to shut down safely when faced with a cyber incident, as we saw in the Middle East in 2017 with the TRISIS/TRITON malware incident, a single unplanned shutdown can wipe out the profits of a refinery or petrochemical plant for the entire year.
Increased Focus on Risk Management
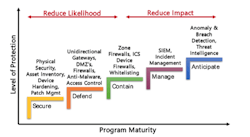
For many end users in manufacturing and critical infrastructure, cybersecurity policy focuses on countering potential threats by reducing exposure to phishing, beefing up password security, etc. ARC Advisory Group’s maturity model for cybersecurity enables end users to measure their own overall level of security and sophistication. Many end users are realizing, however, that they cannot possibly address every threat all the time and are thus looking at the science of risk management to help prioritize their efforts.
Lower maturity levels: Actions are about reducing likelihood of an attack.
Higher maturity levels: Actions are about reducing impacts of an attack.
Cyber Risk No Longer Exclusive of Physical Risk
Significantly, cybersecurity risk is no longer limited to the cyber world but can have very real consequences in the physical world. These risks exist along a spectrum of severity that ranges from simple unplanned downtime in operations to a plant explosion or release of hazardous materials. Stuxnet, which proved that physical assets like nuclear centrifuges can be destroyed through cyber-attacks, gave birth to this realization. And even though the initial attack resulted in a safe plant shutdown, TRITON/TRISIS malware showed that process safety systems could be compromised and reprogrammed maliciously so as not to shut down a plant or process in case of an abnormal situation.
Since the malware and attackers will only get more sophisticated over time, we can no longer view safety and cybersecurity as separate domains.
Standard Risk Management Approaches from the IT World
The IT world is no stranger to standard risk management approaches for cybersecurity. FAIR (Factor Analysis of Information Risk), for example, is an established international standard quantitative model for cybersecurity and operational risk. It provides a model for understanding, analyzing,and quantifying information risk in financial terms.
Components of a FAIR Risk Assessment. Source: FAIR Institute
The FAIR approach for risk management has been adopted by RiskLens, a provider of cyber-risk quantification software that helps achieve digital resiliency by managing cyber risk from the business perspective. FAIR is supported by an open consortium of which The Open Group is a key member and supporter. The Open Group has also introduced the Open FAIR Body of Knowledge, together with a certification program for risk analysts.
Aside from FAIR, many service providers, insurance companies and software companies will measure cyber risk and/or offer solutions to reduce that risk. These include Lloyds Register, KDM Analytics, Maxxsure, Hartford Steam Boiler and others.
HAZOP and PHA Approaches: from Safety to Cybersecurity
Risk assessment methodologies and scoring systems for cybersecurity in ICS/SCADA and OT in general are also finding increased traction. Several suppliers that compete in the process safety lifecycle management space are applying their knowledge of process hazard analysis and risk management to cybersecurity.
AE Solutions, for example, has developed a cybersecurity risk assessment methodology based on IEC 62443 requirements. This method links potential threat scenarios with known vulnerabilities and existing countermeasures along with consequence analysis to produce an overall model of cyber risk. Exida offers a process hazard analysis (PHA)-based tool that engineering and other plant personnel can deploy in project, process safety, information technology, and process control activities. Kenexis’ software for performing process hazards analysis (PHA) such as HAZOP and LOPA includes features that allow a security PHA review (SPR) to be performed.
Coordination Between Standards
In 2002, the International Society for Automation (ISA) made the deliberate decision to commission the ISA99 committee to develop standards related to industrial cybersecurity that would have implications for existing standards in the portfolio. The alternative would have been to ask all other committees to incorporate security retroactively into already-published standards.
As a consequence, standards efforts for manufacturing at the OT level are separated into the ISA/IEC 62443 cybersecurity-related set of standards and the ISA-84/IEC 61508 and 61511 efforts related to process safety. The ISA99 work group 7 and ISA84 work group 9 are liaising to coordinate the treatment of safety and security between these two committees. The intersection of security and safety is one of the fundamental concepts that form the basis of the ISA/IEC 62443 standards.
Addition of Physical Security
End users are also discovering that physical security, cybersecurity and safety all overlap. Increasingly, access control systems, video surveillance systems, employee geolocation tagging solutions and other technologies are being looked at from a holistic perspective alongside cybersecurity and safety solutions. New technology approaches like the Internet of Things (IoT) are making it much easier to combine information from these systems to create a better overall picture of physical security, cybersecurity, and both process and overall safety.
Recommendations
The convergence of safety and cybersecurity is real and happening now. Both present significant cost, impact, and risk for the industrial and infrastructure worlds. As attacks and malware become more sophisticated, the risk to human life through disruption of industrial operations due to a cyber-attack is rapidly approaching that of other plant incidents. Cybersecurity should be considered as a potential cause of failure alongside other factors, such as human error or failures of control systems, instrumentation, and valves.
The safety and cybersecurity disciplines have a lot to learn from each other. This cross-discipline sharing of knowledge has already advanced the industry from the increased use of cyber-PHA and HAZOP for cybersecurity. End users should consider forming a cross-functional team or group to address physical-, cyber-, and safety-related risks, or - at a minimum - make sure that existing discipline-specific teams confer on a regular basis. End users should also educate themselves on the emerging blended risk analysis approaches. Some of this is described in the 62443-3-2 standard, which has been approved by ISA and is currently in ballot by IEC.
Larry O'Brien, Vice President, ARC Advisory Group, joined ARC in 1993 as a junior analyst covering the field device market. Since then, he has covered distributed control systems, fieldbus, automation services, process safety systems, SCADA systems, collaborative process automation systems, and -- more recently -- industrial cybersecurity and smart cities. Larry has served on several ISA committees and a three-year stint as global marketing manager for the Fieldbus Foundation. You can email him at [email protected].